Recent Catalysts in Infrastructure Extortion
The global cyber threat landscape has undergone a fundamental transformation, shifting from isolated data theft to large-scale infrastructure extortion. Threat actors have moved beyond “smash-and-grab” tactics to targeting the underlying service providers and cloud integrations upon which the modern enterprise relies. By compromising core infrastructure, entities like ShinyHunters exert maximum pressure on victims, threatening not just data privacy but the operational continuity of entire sectors. This evolution has redefined corporate vulnerability; a single breach at a third-party host now creates a cascading crisis for thousands of downstream organizations.
The May 2026 infiltration of Instructure (Canvas) exemplifies this infrastructure collapse. Part of a broader “wholesale auction” involving 800 million records across multiple global entities, this incident targeted the backbone of higher education.
Global Impact: Over 9,000 schools and universities worldwide were affected, impacting millions of users.
Targeted High-Profile Institutions: Explicit extortion demands were issued to the University of Pennsylvania (UPenn), Duke, Harvard, MIT, and Colorado State University.
The Ultimatum: A hard deadline of May 12, 2026, was set for a negotiated settlement before the leak of billions of private messages, student IDs, and enrollment data.
Operational Disruption: The breach occurred on May 7, just hours before UW-Madison’s last day of finals, forcing a platform-wide shutdown during a critical academic window.
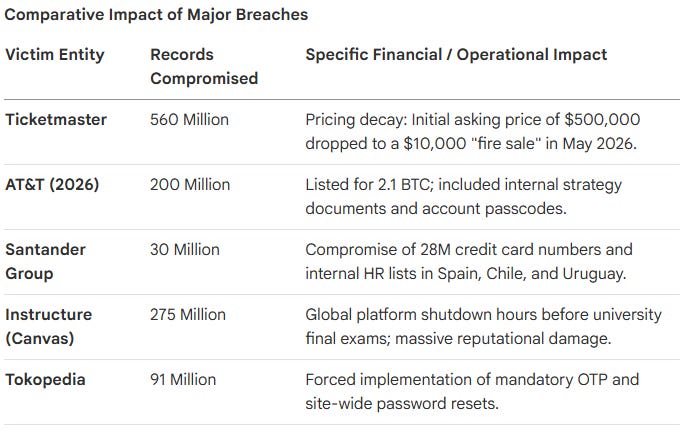
While the 2024 AT&T breach saw the company reportedly pay a $370,000 bitcoin ransom to the intermediary “Reddington” for data deletion, the May 2026 auction represents a significant escalation. This later campaign listed 200 million AT&T records for 2.1 BTC, notably including sensitive internal strategy documents and account passcodes. The “So What?” for executive leadership is the heightened legal and regulatory peril posed by the Ransomware and Financial Stability Act 2024. This legislation prohibits major firms from making ransom payments exceeding $100,000 without federal authorization, significantly complicating the recovery calculus. Furthermore, the 2024 Ticketmaster/Live Nation breach, which compromised 560 million customer records, highlights the massive scale of PII now circulating in the underground economy. These incidents serve as the necessary precursor to understanding the identity and predatory methodology of the ShinyHunters entity.
Defining ShinyHunters: From Hacking Group to Behavioral Pattern
Defining a modern threat actor is increasingly difficult as identities fluctuate across decentralized forums and various pseudonyms. In the professional intelligence community, “ShinyHunters” is no longer viewed as a traditional, static hacking group. Instead, as noted by researchers at Vectra AI, it represents a “pattern-based” threat model. ShinyHunters is a brand or behavioral signal used at the moment of extortion to signify a specific methodology: the exploitation of third-party supply chains and the abuse of legitimate identities.
The group is deeply embedded in “The Com,” a decentralized ecosystem largely comprised of teens and young adults based in the US and the UK. This demographic is characterized by high technical proficiency and unpredictable motivations, making them a volatile strategic risk.
BreachForums has functioned as the primary auction house for this entity, surviving multiple law enforcement takedowns. Leadership transitions illustrate the resilience of this ecosystem:
pompompurin (Conor Brian Fitzpatrick): Founded the original BreachForums; currently serving a prison sentence following violations of supervised release.
Baphomet: A successor administrator who maintained the forum’s infrastructure alongside ShinyHunters.
IntelBroker (Kai West): A prominent actor arrested in France in early 2025; West was a high-profile administrator and contributor before his indictment for multiple cybercrimes.
The ShinyHunters brand is a persistent signal of an identity-based attack methodology that prioritizes valid access over malware, a tactic that has defined their historical trajectory.
Chronology of a Digital Spree: A Multistage History
Tracking a threat actor’s history is essential to identifying the shift from opportunistic database theft to strategic infrastructure compromise.
The Era of Forums (2020–2024): Database Spree
May 2020: Initial emergence; breach of Tokopedia (91M records) and theft of 500GB of private source code from Microsoft GitHub.
July 2020: Breach of Wattpad (270M records) and the digital banking service Dave (7M).
2021–2023 Expansion: Pivot toward global services and Indian fintech, targeting BigBasket (20M records sold for $40,000), NitroPDF (77M records), and Pixlr (19M records). The group publicly criticized these firms for “poor cyber hygiene” regarding plaintext data storage.
The Era of Identity & SaaS Supply Chain Attacks (2025–2026) The group evolved into a sophisticated supply chain predator. The 2025-2026 Salesforce campaign targeted approximately 400 companies, including Google, FedEx, Disney, and Marriott, using stolen OAuth tokens.
The “So What?” layer centers on the Anodot exploit. In 2026, ShinyHunters extracted authentication tokens from Anodot, a SaaS analytics provider. These tokens allowed for valid access to downstream environments in Snowflake and BigQuery. Because the attackers utilized trusted credentials, they bypassed Snowflake’s defenses entirely without needing to exploit a vulnerability in the platform itself. This method allowed them to exfiltrate data from high-value targets like Rockstar Games and Vimeo, behaving exactly like a legitimate application. This history demonstrates that the group has achieved a level of unchecked reach that translates into massive, systemic financial liabilities.
The Business Ledger: Quantifying the Cost of Victimization
Data breach costs in the technology and financial sectors often dwarf initial ransom demands due to operational paralysis and the compounding weight of regulatory fallout.
Quantitative impact data from IBM’s 2024 report highlights the following:
Industry Ranking: Healthcare remains the most expensive sector for breaches, with Financial Services ranking second at an average cost of $6.08 million per incident.
Skyrocketing Scale: For large-scale breaches (50M+ records), costs reached an average of 375million∗∗,representinga∗∗40 million increase between 2023 and 2024.
Regulatory Compounding: Beyond remediation, containment delays lead to fines under GDPR, CCPR, and LGPD that frequently outpace initial forensic expenses.
Qualitative costs further erode shareholder value. Carnival Corporation faced multiple class-action lawsuits citing weak cybersecurity controls after a ShinyHunters-linked breach of 8.7 million records. Similarly, MGM Resorts was forced to pay a $45 million settlement in 2025 following its 2023 breach, which saw stock valuations dip significantly.
The “window of vulnerability” is a critical driver of these costs. Organizations in the financial sector take an average of 168 days to identify a breach and 51 days to contain it. This nearly seven-month window provides actors with ample time for reconnaissance and credential harvesting, maximizing enterprise damage.
The Persistence of the Pattern
The FBI and French law enforcement (BL2C) have successfully dismantled much of the BreachForums infrastructure, resulting in the arrests of IntelBroker and other key ShinyHunters affiliates. In a signed PGP message, the group itself admitted that “the era of forums is over” and warned that remaining reboots of these sites should be regarded as law enforcement “honeypots.”
However, the threat has not dissipated; it has refined. ShinyHunters represents the terminal transition to “Identity Abuse,” where the primary goal is not the deployment of malware, but the success of an authentication flow. By leveraging infostealer logs, session hijacking, and stolen tokens, they masquerade as benign identities to navigate the cloud supply chain.
Defensive Imperatives:
SaaS-to-SaaS OAuth Auditing: Moving beyond standard IAM, organizations must rigorously audit OAuth scopes and third-party integrations (e.g., Anodot, Salesforce) to prevent token-based lateral movement.
Rapid Token Deactivation Protocols: Develop automated playbooks for the immediate rotation of application keys and deactivation of compromised tokens the moment a third-party breach is detected.
AI-Driven Identity Analytics: Invest in behavioral detection that identifies anomalies after a successful login. Verification must be continuous, as traditional MFA is no longer an absolute barrier against session hijacking.
ShinyHunters may have abandoned the forum model, but the pattern of masquerading as a trusted identity remains the single most potent threat to global digital infrastructure.